PDF) The RWTH Large Vocabulary Speech Recognition System for Spontaneous Speech | Stephan Kanthak - Academia.edu
PDF) Bibliographies and Literature Reviews: Goals, Issues and Directions in Machine Learning of Natural Language and Ontology

SZZ Algorithm Feasible Automatic Solution for the Bug Problem by Heider Jeffer & Prof. Barbara Russo - YouTube

Principles of Public Key Cryptography. Applications of Public Key Cryptography. Security in Public Key Algorithms - PDF Free Download

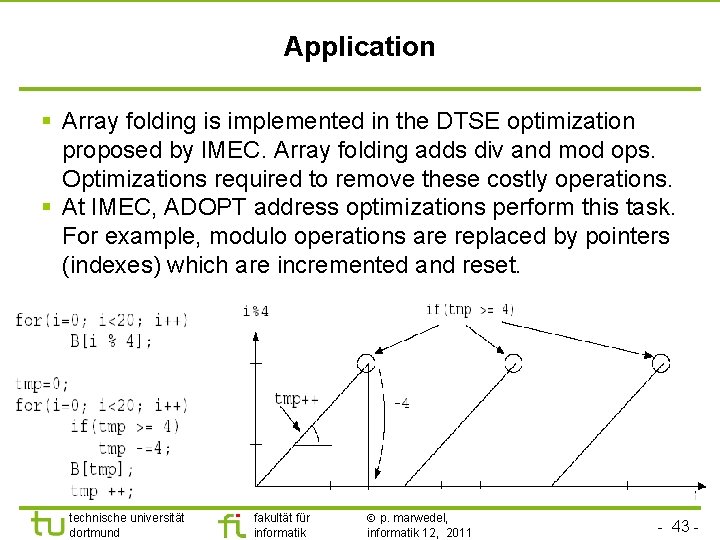
1 - P. Marwedel, Univ. Dortmund, Informatik 12, 05/06 Universität Dortmund Context Codesign: Considering HW and SW to generate an efficient system. - ppt download











![FSX P3D] Aerosoft - Menorca LEMH Evolution Mod chadmard FSX P3D] Aerosoft - Menorca LEMH Evolution Mod chadmard](http://docplayer.org/docs-images/47/9564758/images/page_3.jpg)